GitHub is the hottest platform visited by hackers, lots of of whom have been hit really hard, together with crypto tasks.

GitHub faced a substantial-scale malware assault with 35,000 “code hits” at the identical time as 1000’s of Solana wallets visited by hackers yesterday morning.
The assault was identified by GitHub developer Stephen Lucy though reviewing a venture he uncovered on Google Search.
I am finding what seems to be a significant malware assault spreading @github.
– Currently more than 35,000 repositories are contaminated
– So far uncovered in tasks together with: crypto, golang, python, js, bash, docker, k8s
– It is extra to npm scripts, docker photographs and set up paperwork pic.twitter.com/rq3CBDw3r9– Stephen Lacy (@stephenlacy) August 3, 2022
“I am finding what seems to be a substantial-scale malware assault.
– More than 35,000 repositories are at this time contaminated.
– So far uncovered in tasks together with: crypto, golang, python, js, bash, docker, k8s.
– Added to npm scripts, docker photographs, and set up documentation pic.twitter.com/rq3CBDw3r9“
So far, there have been platforms impacted by the assault, together with crypto tasks. The assault targets docker photographs, doc settings, and npm scripts, which are a hassle-free way to bundle widespread shell commands for a venture.
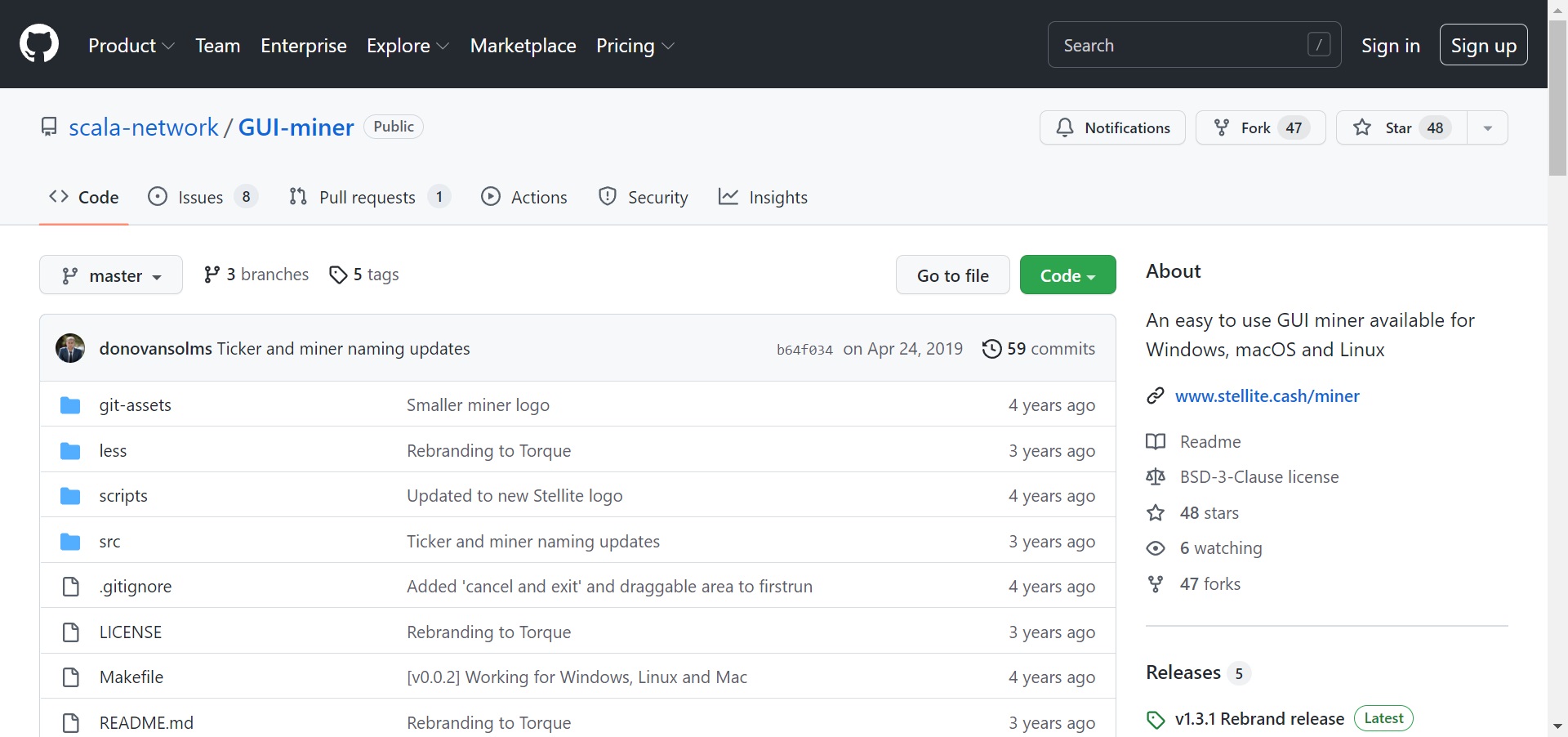
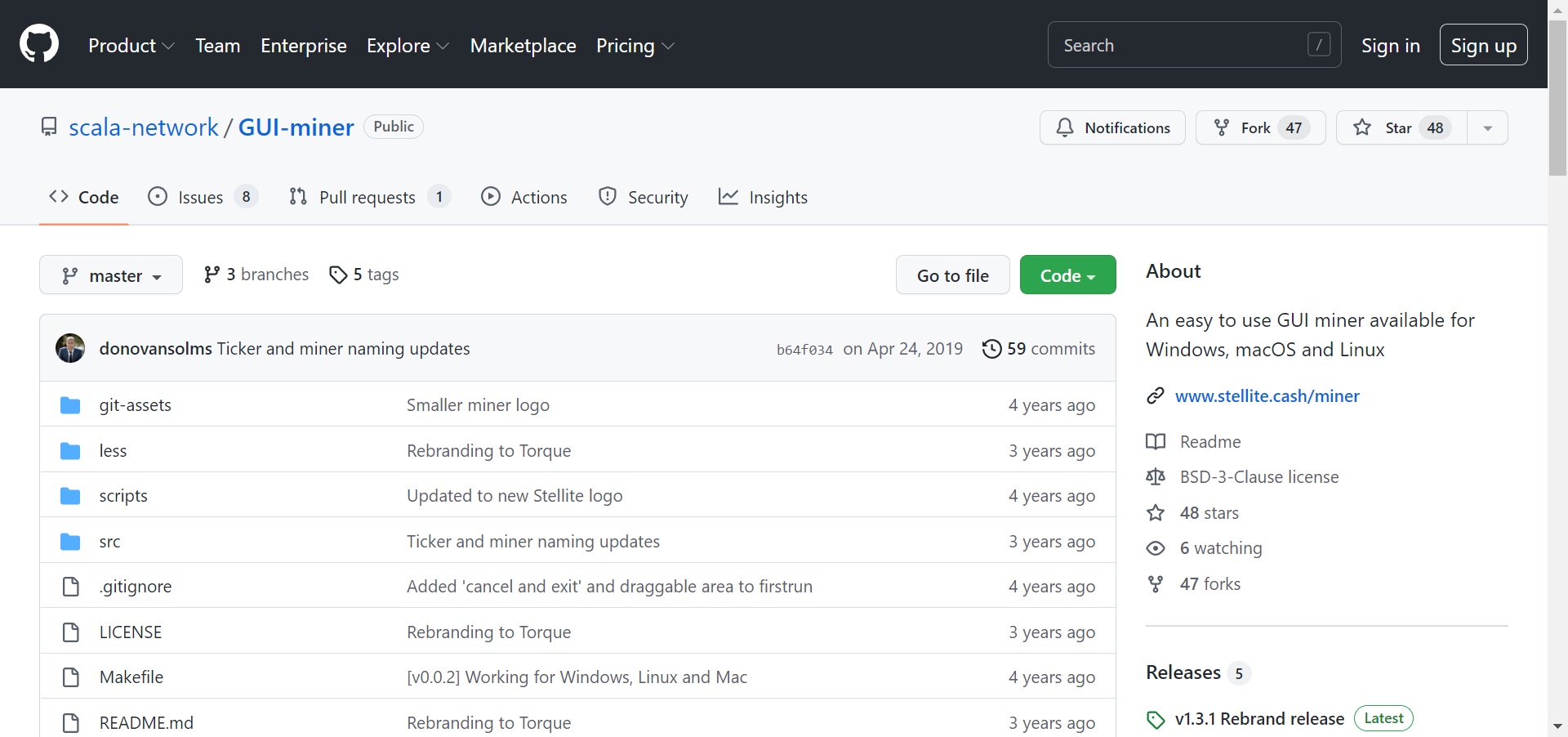
To trick developers into gaining entry to vital information, an attacker 1st produces a fake archive (one particular that includes all venture files and the revision background of every file) and sends copies of reputable tasks to GitHub. For illustration, the following two photographs:
Many of these cloned repositories are deleted as “pull requests / pull requests”. This necessity makes it possible for developers to notify some others of alterations they have submitted to a branch in a repository on GitHub.
Once a developer falls prey to a malware assault, the total atmosphere variable (ENV) of the script, application or laptop (electronic application) is sent to the attacker’s server. ENV consists of protection crucial, AWS entry crucial, cryptographic crucial …
The developer reported the situation to GitHub and recommended developers to indicator revisions to the repository on GPG. GPG keys include an additional layer of protection to GitHub accounts and software program tasks by delivering a way to confirm that all revisions are from a trusted supply.
Just a couple of days soon after the finish of the month, there have been lots of “cockroach” protection incidents in the cryptocurrency business. Interestingly, the Nomad cross-chain bridge was retired by hackers on August two, leaving consumers a good deal of grief and dragging along lots of connected platforms. Not owning time to recover, the marketplace was rocked this morning by the information that the Solana network had a major protection flaw, but the venture has not still identified the origin of the hack, but has only offered the preliminary lead to soon after lots of hrs. of investigation. .
Synthetic currency 68
Maybe you are interested:







